What is DKIM Authentication?
DKIM, which stands for DomainKeys Identified Mail, is an email authentication method designed to detect email spoofing and prevent phishing scams. It works by allowing an organization to take responsibility for their emails through digital signatures.
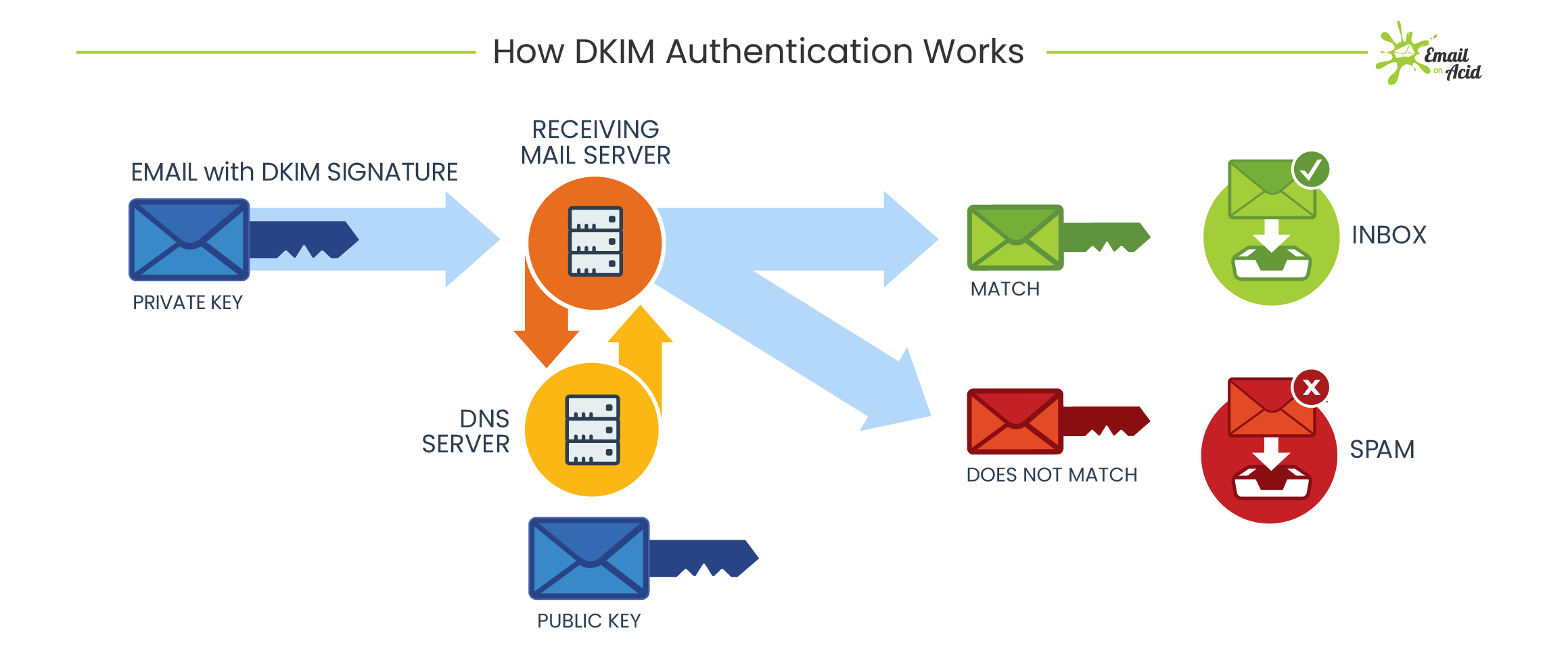
When an email is sent using DKIM authentication, the sender’s email server signs the email with a private key. This signature is then verified by the recipient’s email server using a public key stored in the organization’s DNS records. If the signatures match, the email is considered legitimate and is delivered to the recipient’s inbox.
DKIM authentication helps to verify the authenticity of email messages and protect against domain spoofing, phishing attacks, and other forms of email fraud. It adds a layer of security to the email communication process and helps build trust between senders and recipients.
How Does DKIM Authentication Work?
DKIM authentication works by adding a digital signature to the header of an email message when it is sent. This digital signature is generated using the sender’s private key and is unique to each message. When the email is received, the recipient’s email server retrieves the public key from the sender’s DNS records and uses it to verify the signature.
If the digital signature matches the message content, the email is considered authentic and is delivered to the recipient’s inbox. If the signature is invalid or missing, the email may be marked as spam or rejected entirely, depending on the recipient’s email provider’s policies.
Benefits of DKIM Authentication
- Prevents email spoofing
- Reduces the risk of phishing attacks
- Increases email deliverability
- Enhances sender reputation
- Builds trust with recipients
Implementing DKIM Authentication
Implementing DKIM authentication involves generating a public/private key pair, adding the public key to the organization’s DNS records, and configuring the email server to sign outgoing messages with the private key. Most email service providers offer built-in support for DKIM authentication, making it easy for organizations to secure their email communication.
By implementing DKIM authentication, organizations can protect their email communication from spoofing attacks, improve email deliverability rates, and build trust with recipients. It is an essential part of an organization’s email security strategy and can help prevent email fraud and maintain a positive sender reputation.
Conclusion
DKIM authentication is a critical tool in the fight against email fraud and phishing scams. By verifying the authenticity of email messages and preventing domain spoofing, DKIM helps organizations build trust with their recipients and protect their brand reputation. Implementing DKIM authentication is a simple yet effective way to enhance email security and ensure that legitimate emails reach their intended recipients.