Vpn and advanced ssh tunneling: Ensuring Security and Privacy Online
Virtual Private Networks (VPNs) and SSH tunneling are two powerful tools that can enhance your online security and privacy. In this article, we will explore the benefits of using both VPNs and advanced SSH tunneling techniques to protect your sensitive information from prying eyes.
Internet privacy is a hot topic these days, with cyber attacks and data breaches becoming increasingly common. Using a VPN can help protect your online activities from being monitored by hackers, government agencies, or internet service providers.
What Is a VPN?
A VPN is a tool that creates a secure and encrypted connection between your device and a remote server. This connection acts as a tunnel, allowing you to browse the internet anonymously and securely.
When you connect to a VPN server, your IP address is masked, and your internet traffic is encrypted. This makes it nearly impossible for anyone to track your online activities or intercept your data.
How Does SSH Tunneling Work?
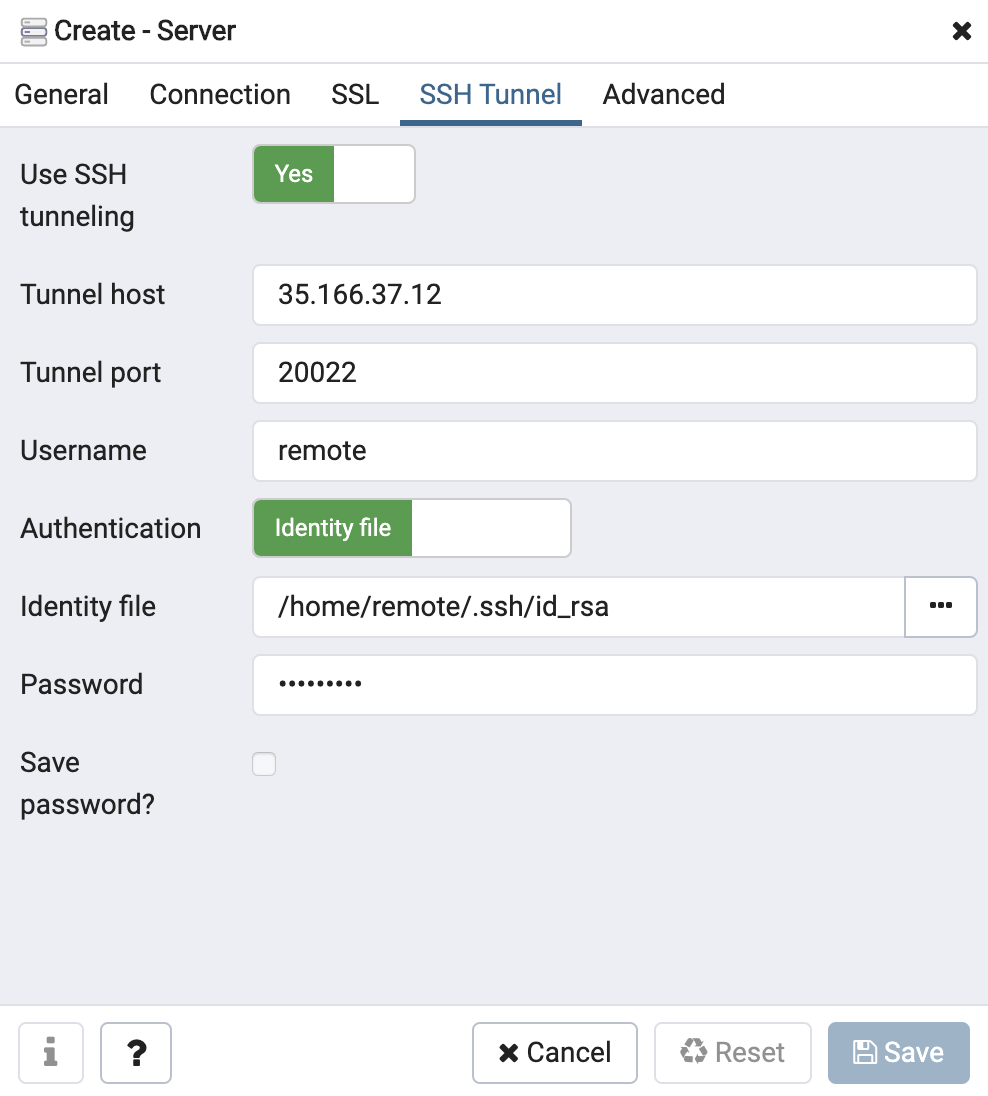
SSH tunneling involves creating a secure connection between your device and a remote server using the Secure Shell (SSH) protocol. This protocol encrypts your data transmission, making it secure from eavesdroppers.
By setting up an SSH tunnel, you can redirect your internet traffic through the encrypted connection, bypassing any potential threats or restrictions on the network. This can be particularly useful when accessing public Wi-Fi hotspots or restricted websites.
Benefits of Using a VPN and SSH Tunneling Together
Using a VPN and SSH tunneling together can provide an extra layer of security for your online activities. By combining these two tools, you can ensure that your data remains encrypted and secure from any potential threats.
Additionally, using a VPN with SSH tunneling can help you bypass censorship or geo-restrictions on certain websites or services. This can be particularly beneficial for users who want to access content that is not available in their region.
Choosing the Right VPN and SSH Tunneling Provider
When selecting a VPN and SSH tunneling provider, it is essential to choose a reputable and reliable service. Look for providers that offer strong encryption protocols, a strict no-logs policy, and a wide selection of server locations.
Additionally, consider the speed and stability of the VPN and SSH tunneling service. A slow connection can hinder your browsing experience, while an unreliable service can expose your data to potential security risks.
Conclusion
In conclusion, using a VPN and advanced SSH tunneling techniques can significantly enhance your online security and privacy. By encrypting your internet traffic and masking your IP address, you can protect your sensitive information from cyber threats and surveillance.
Remember to choose a reputable VPN and SSH tunneling provider to ensure that your data remains secure and encrypted at all times. Stay safe online!