How to Set Up a Honeypot
Are you looking to enhance your cybersecurity defenses? Setting up a honeypot can be an effective way to detect and track malicious activities on your network. In this article, we will guide you through the process of setting up a honeypot to strengthen your security posture.
What is a Honeypot?
A honeypot is a cybersecurity mechanism designed to lure attackers by mimicking vulnerable systems or services. This decoy system appears as a legitimate target to malicious actors, allowing security professionals to monitor and analyze their tactics, techniques, and procedures.
Types of Honeypots
There are several types of honeypots, including:
- Research honeypots: Used to collect threat intelligence and study attacker behavior.
- Production honeypots: Deployed in live environments to deceive and divert malicious activities.
- High-interaction honeypots: Offers extensive interaction with attackers to gather detailed information.
- Low-interaction honeypots: Provides limited interaction to minimize risk and resource consumption.
Setting Up Your Honeypot
Follow these steps to set up a honeypot effectively:
1. Define Your Objectives
Before deploying a honeypot, clearly define your objectives and goals. Determine what you aim to achieve by setting up a honeypot and how it aligns with your overall security strategy.
2. Select the Right Type of Honeypot
Choose a honeypot type based on your objectives and resources. Consider factors such as the level of interaction required, the complexity of deployment, and the information you wish to gather.
3. Design and Deploy Your Honeypot
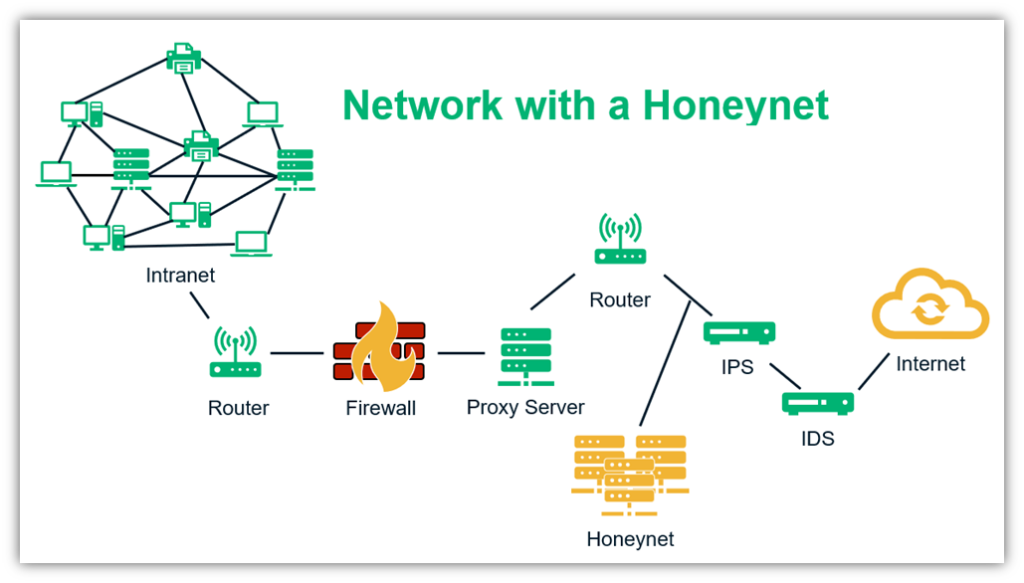
Design your honeypot to mimic a realistic target, ensuring that it appears enticing to attackers. Deploy the honeypot in a segregated network segment to isolate it from critical systems and prevent unauthorized access.
4. Monitor and Analyze Activity
Once your honeypot is active, monitor and analyze the incoming traffic. Look for signs of malicious activity, such as unauthorized access attempts, unusual network connections, or suspicious file transfers.
Benefits of Using a Honeypot
Setting up a honeypot offers several benefits, including:
- Enhancing threat intelligence: Gather valuable insights into attacker tactics and intentions.
- Early detection of threats: Identify potential threats before they impact critical systems.
- Improved incident response: Develop effective response strategies based on observed attacker behavior.
- Reduced security risks: Proactively identify and address vulnerabilities in your network.
Conclusion
By setting up a honeypot, you can strengthen your cybersecurity defenses and gain valuable insights into potential threats. Follow the steps outlined in this article to effectively deploy a honeypot and enhance your security posture.