The Allure of Honeypot VMware: Enhancing Your Virtual Environment Security

Virtualization technology has revolutionized the way we create, test, and deploy applications in the digital age. As we embrace this innovative technology, it’s essential to prioritize cybersecurity to safeguard our virtual environments from potential threats. One powerful tool in our security arsenal is the honeypot VMware.
But what exactly is a honeypot VMware, and how can it benefit your virtual environment? Let’s delve into the world of honeypots and explore how they can enhance your cybersecurity posture.
Understanding Honeypots
A honeypot is a cybersecurity measure designed to deceive attackers into interacting with a simulated system or network. By masquerading as a legitimate target, honeypots lure cybercriminals into disclosing their tactics, techniques, and procedures (TTPs) without compromising the actual production environment.
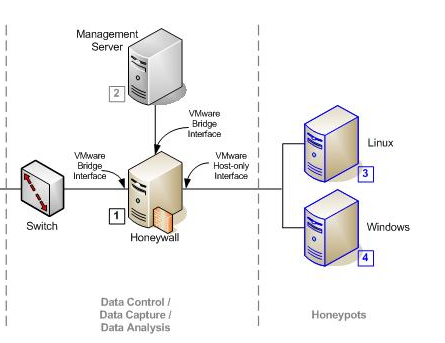
When it comes to virtual environments, honeypot VMware is a specialized type of honeypot tailored for VMware platforms. It’s strategically deployed within your virtual infrastructure to attract and intercept malicious activities, allowing you to gather valuable threat intelligence while minimizing risks to your critical systems.
The Importance of Honeypot VMware
As organizations increasingly rely on virtualized environments to run their workloads, the need for robust security measures becomes paramount. Honeypot VMware offers several key benefits for enhancing your virtual environment security:
- Early Threat Detection: Honeypots can detect and alert you to potential security incidents before they escalate, giving you a proactive advantage in mitigating cyber threats.
- Threat Intelligence Gathering: By analyzing attacker behavior and tactics, you can gain valuable insights into emerging threats and vulnerabilities specific to your VMware environment.
- Decoy System Protection: Honeypot VMware acts as a sacrificial lamb, diverting attackers’ attention away from your critical systems and applications, reducing the risk of data breaches.
Best Practices for Implementing Honeypot VMware
While honeypot VMware can significantly bolster your virtual environment security, it’s essential to follow best practices to maximize its effectiveness:
- Strategic Placement: Deploy honeypots in areas of your VMware infrastructure where they are most likely to attract malicious actors, such as vulnerable network segments or high-traffic servers.
- Regular Monitoring: Continuously monitor and analyze honeypot VMware data to identify patterns of unauthorized access or intrusions, enabling timely responses to potential threats.
- Integration with SIEM: Integrate honeypots into your Security Information and Event Management (SIEM) system to correlate threat intelligence with broader security monitoring efforts and enhance incident response capabilities.
In Conclusion
Honeypot VMware is a valuable tool for fortifying your virtual environment against cyber threats. By implementing honeypots strategically and following best practices, you can enhance your cybersecurity posture, detect threats early, and gather actionable threat intelligence to safeguard your VMware infrastructure.
As you navigate the complex landscape of virtualization security, consider integrating honeypot VMware into your defense strategy to stay one step ahead of cyber adversaries. Protect your virtual assets, preserve data integrity, and maintain the trust of your stakeholders with this proactive cybersecurity solution.