Understanding Drupal Brute Force Attacks
Drupal is a powerful content management system that is widely used by website developers around the world. However, like any other platform, Drupal is vulnerable to brute force attacks if the necessary security measures are not in place. In this article, we will delve into what Drupal brute force attacks are, how they work, and most importantly, how you can protect your Drupal website from falling victim to such attacks.
What is a Brute Force Attack?
A brute force attack is a cybersecurity attack that relies on trial and error to crack passwords and gain unauthorized access to a system. In the context of Drupal, a brute force attack involves an attacker using automated scripts to systematically guess usernames and passwords until the correct combination is found. Once the attacker gains access to the Drupal website, they can wreak havoc by stealing sensitive data, defacing the website, or installing malicious software.
How Do Drupal Brute Force Attacks Work?
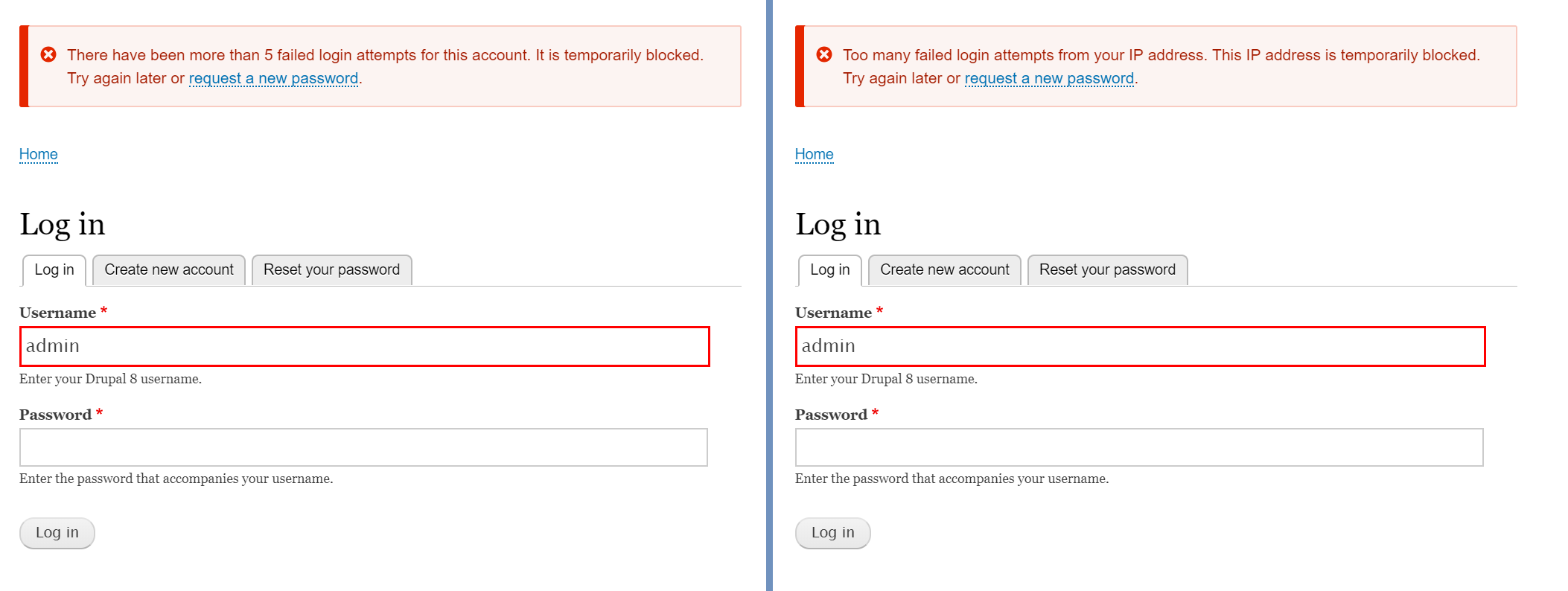
Drupal brute force attacks typically target the login page of a website, where users are required to enter their username and password to access the platform. The attacker uses automated tools to generate a massive number of login attempts in a short period of time, hoping to guess the correct credentials through sheer luck or persistence.
Once the attacker gains access to the Drupal website, they can carry out a variety of malicious activities, including:
- Stealing sensitive user data
- Defacing the website with inappropriate content
- Installing malware or ransomware
- Using the website to launch further attacks
Protecting Your Drupal Website
As a website owner or developer, it is crucial to take proactive steps to protect your Drupal website from brute force attacks. Here are some effective strategies to enhance the security of your Drupal platform:
- Use strong and unique passwords for user accounts
- Implement two-factor authentication for added security
- Limit the number of login attempts allowed per IP address
- Regularly update Drupal core and modules to patch any security vulnerabilities
- Monitor your website for any suspicious activity and take immediate action if an attack is detected
- Utilize security plugins or services to bolster your website’s defenses
By following these best practices and staying vigilant, you can significantly reduce the risk of falling victim to a Drupal brute force attack. Remember, the security of your website is in your hands, so make sure to prioritize cybersecurity to safeguard your online presence.
Stay safe and secure!